
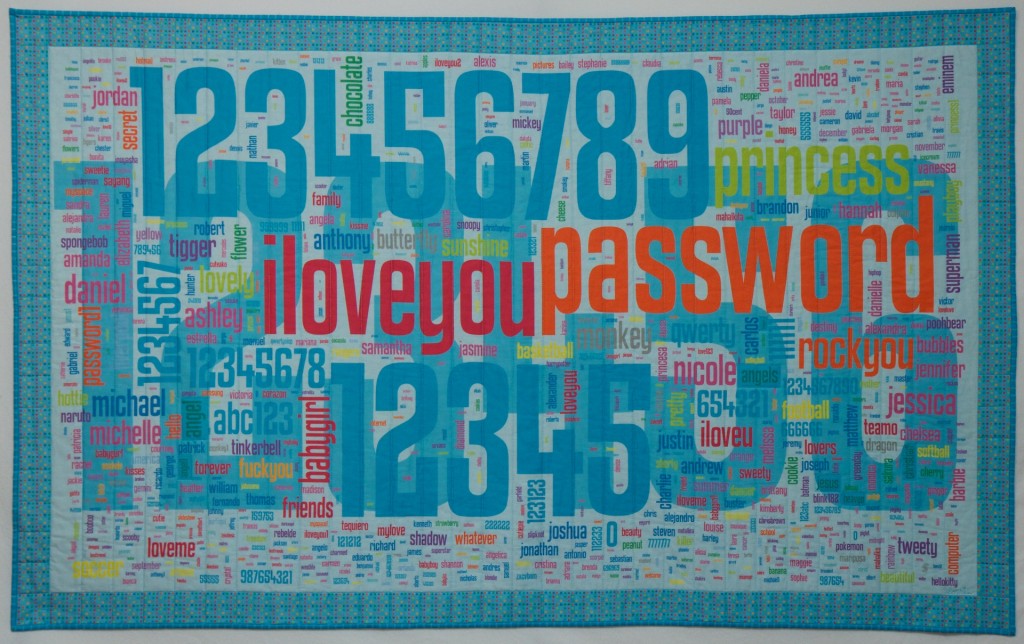
Security Blanket by Lorrie Faith Cranor, machine quilted, digitally
printed cotton fabric, 63.5" x 39", appeared in
the February
7, 2014
issue of Science Magazine.
Passwords ties, fabric,
and other fashion and furnishings
now available!
Passwords and Authentication Research
To combat both the inherent and user-induced weaknesses of text-based passwords, administrators and organizations typically institute a series of rules – a password policy – to which users must adhere when choosing a password. There is consensus in the literature that a properly-written password policy can provide an organization with increased security. There is, however, less accord in describing just what such a well-written policy would be, or even how to determine whether a given policy is effective. Although it is easy to calculate the theoretical password space that corresponds to a particular password policy, it is difficult to determine the practical password space. Users may, for example, react to a policy rule requiring them to include numbers in passwords by overwhelmingly picking the same number, or by always using the number in the same location in their passwords. There is little published empirical research that studies the strategies used by actual users under various password policies. In addition, some password policies, while resulting in stronger passwords, may make those passwords difficult to remember or type. This may cause users to engage in a variety of behaviors that might compromise the security of passwords, such as writing them down, reusing passwords across different accounts, or sharing passwords with friends. Other undesirable side effects of particular password policies may include frequently forgotten passwords. In fact, the harm caused by users following an onerously restrictive password policy may be greater than the harm prevented by that policy. In this project, we seek to advance understanding of the factors that make creating and following appropriate password policies difficult, collect empirical data on password entropy and memorability under various password policies, and propose password policy guidelines to simultaneously maximize security and usability of passwords. We also explore the security and usability of some new types of passwords.
Faculty: Lujo Bauer, Nicolas Christin, Lorrie Cranor
Tools and demos
- Open Source Password Meter - We developed a password meter that provides data-driven, actionable feedback based on our research. Try out our online demo or download the source code from Github. This password meter runs in the user's web browser; feedback is returned as the user types, without sending the password over the Internet. The meter uses our neural network approach to password analysis, which won a best paper award at USENIX 2016. Our paper on the meter design and evaluation won a best paper award at CHI 2017.
- Password Guessability Service - Our free service for the research community that estimates plaintext passwords' guessability: how many guesses a particular password-cracking algorithm with particular training data would take to guess a password.
- The Password Game - a quiz about password security based on our research
Research talks
- The Continuing Quest for Secure and Usable Passwords - Sean Segreti and Blase Ur's talk at Passwordscon 2014, August 5, 2014
- iloveyou password 123456 - Lorrie Cranor's TEDxCMU talk on passwords, March 2, 2014.
Blogs and magazine articles
- L. Cranor, B. Ur, L. Bauer, M. Mazurek, and N. Christin. Choose better passwords with the help of science. The Conversation, August 20, 2017.- Reprinted in the Washington Post, September 8, 2017
- L. Cranor, Time to rethink mandatory password changes, Tech@FTC, March 2, 2016.
- B. Ur, P.G. Kelley, S. Komanduri, J. Lee, M. Maass, M.L. Mazurek, T. Passaro, R. Shay, T. Vidas, L. Bauer, N. Christin, L.F. Cranor, S. Egelman, and J. Lopez. Helping Users Create Better Passwords. ;login: Vol 37, No. 6, December 2012.
News
- Passwords research group awarded the 2020 Allen Newell Award for Research Excellence by Daniel Tkacik, May 22, 2020.
- New tool teaches you how to set stronger passwords by Freia Lobo, May 9, 2017, Mashable
- How to create a strong password: This online 'password meter' tool can help you fend off hackers, By Jason Murdock May 9, 2017, International Business Times
- The AI that can help you choose a safe password: Interactive site offers help to keep hackers at bay by Stacy Liberatore, May 8, 2017, Daily Mail
- Researchers unveil new password meter
- New Meter Will Change How Users Create Passwords, May 8, 2017.
- NATO partners with CyLab to increase password security, June 23, 2016. CyLab News
- People Understand How to Make Good Passwords, But Still Don't, Motherboard, May 13, 2016.
- Users’ Perceptions of Password Security Do Not Always Match Reality, CyLab News, May 11, 2016.
- Why changing your password regularly may do more harm than good By Andrea Peterson, The Washington Post, March 2, 2016.
- What goes into a good, secure password? CMU Engineering podcast, Daniel Tkacik interviews Lorrie Cranor, October 2015.
- Wolverton: Putting the password problem in perspective By Troy Wolverton, San Jose Mercury News, February 6, 2015.
- What makes a good password? The Naked Scientists, September 16, 2014 [radio broadcast on Broadcast on BBC Cambridgeshire, BBC 5 Live and Australian ABC]
- The best defense against hackers is...paper? by Timothy B. Lee, Vox, April 16, 2014.
- Password complexity rules more annoying, less effective than lengthy ones by Casey Johnston, Ars Technica, June 28, 2013.
- Password length is more beneficial than complexity by Deborah M. Todd, Pittsburgh Post-Gazette, August 30, 2012.
- Building a Better Password by Nick Summers, NEWSWEEK published Oct 9, 2009 from the magazine issue dated Oct 19, 2009.
Research papers
Joshua Tan, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor Practical Recommendations for Stronger, More Usable Passwords Combining Minimum-strength, Minimum-length, and Blocklist Requirements, CCS 2020, November 9-13, 2020.
Sruti Bhagavatula, Lujo Bauer, and Apu Kapadia. (How) Do People Change Their Passwords After a Breach? 2020 Workshop on Technology and Consumer Protection (ConPro '20), May 21, 2020.
Sarah Pearman, Shikun Aerin Zhang, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor. Why people (don’t) use password managers effectively. SOUPS 2019.
Hana Habib, Pardis Emami Naeini, Summer Devlin, Maggie Oates, Chelse Swoopes, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor. User Behaviors and Attitudes Under Password Expiration Policies. Fourteenth Symposium on Usable Privacy and Security (SOUPS 2018), Baltimore, MD, pp. 13-20.
J. Colnago, S. Devlin, M. Oates, C. Swoopes, L. Bauer, L. Cranor, and N. Christin. "It's Not Actually That Horrible": Exploring Adoption of Two-Factor Authentication at a University, CHI 2018 pages 456:1--456:11, 2018.
Sarah Pearman, Jeremy Thomas, Pardis Emami Naeini, Hana Habib, Lujo Bauer, Nicolas Christin, Lorrie Faith Cranor, Serge Egelman, and Alain Forget. Let’s go in for a closer look: Observing passwords in their natural habitat. In Proceedings of the 24th ACM Conference on Computer and Communications Security (CCS’17). 2017.
Sean Segreti, William Melicher, Saranga Komanduri, Darya Melicher, Richard Shay, Blase Ur, Lujo Bauer, Nicolas Christin, Lorrie Cranor, and Michelle Mazurek. Diversify to Survive: Making Passwords Stronger with Adaptive Policies. SOUPS 2017, Santa Clara, CA, July 12-14, 2017.
Blase Ur, Felicia Alfieri, Maung Aung, Lujo Bauer, Nicolas Christin, Jessica Colnago, Lorrie Faith Cranor, Henry Dixon, Pardis Emami Naeini, Hana Habib, Noah Johnson, and William Melicher. 2017. Design and Evaluation of a Data-Driven Password Meter. CHI 2017. [video preview] BEST PAPER AWARD
H. Habib, J. Colnago, W. Melicher, B. Ur, S. Segreti, L. Bauer, N. Christin, and L. Cranor. Password Creation in the Presence of Blacklists. USEC 2017, February 26, 2017, San Diego, CA.
Blase Ur. Supporting Password-Security Decisions with Data. PhD thesis, Societal Computing, September 2016.
W. Melicher, B. Ur, S. Segreti, S. Komanduri, L. Bauer, N. Christin, L. Cranor. Fast, Lean, and Accurate: Modeling Password Guessability Using Neural Networks. USENIX Security, August 10-12, 2016, Austin, TX. BEST PAPER AWARD
W. Melicher, D. Kurilova, S. Segreti, P. Kalvani, R. Shay, B. Ur, L. Bauer, N. Christin, L. F. Cranor, and M. L. Mazurek. Usability and security of text passwords on mobile devices. CHI'16.
B. Ur, J. Bees, S. Segreti, L. Bauer, N. Christin, and L. F. Cranor. CHI'16. Do users' perceptions of password security match reality? CHI 2016 Honorable Mention. [video teaser, online game]
R. Shay, S. Komanduri, A. Durity, P. Huh, M. Mazurek, S. Segreti, B. Ur, L. Bauer, N. Christin, L. Cranor. Designing Password Policies for Strength and Usability. ACM Trans. Inf. Syst. Secur. 18, 4, Article 13 (May 2016), 34 pages.
S. Komanduri. Modeling the Adversary to Evaluate Password Strength with Limited Samples, PhD Thesis (COS), February 2016.
B. Ur, S. Segreti, L. Bauer, N. Christin, L. Cranor, S. Komanduri, D. Kurilova, M. Mazurek, W. Melicher and R. Shay. Measuring Real-World Accuracies and Biases in Modeling Password Guessability. USENIX Security Symposium 2015. [1-minute lightning talk video]
B. Ur, F. Noma, J. Bees, S. Segreti, R. Shay, L. Bauer, N. Christin, L Cranor. "I Added '!' At The End To Make It Secure": Observing Password Creation in the Lab. SOUPS2015.
R. Shay, L. Bauer, N. Christin, L. Cranor, A. Forget, S. Komanduri, M. Mazurek, W. Melicher, S. Segreti, and B. Ur. A Spoonful of Sugar? The Impact of Guidance and Feedback on Password-Creation Behavior. CHI 2015.
R. Shay. Creating Usable Policies for Stronger Passwords with MTurk, PhD Thesis (COS), February 2015.
Chandrasekhar Bhagavatula, Blase Ur, Kevin Iacovino, Su Mon Kywe, Lorrie Faith Cranor, Marios Savvides. Biometric Authentication on iPhone and Android: Usability, Perceptions, and Influences on Adoption. USEC 2015, February 8, 2015.
Saranga Komanduri, Richard Shay, Lorrie Faith Cranor, Cormac Herley, and Stuart Schechter. Telepathwords: Preventing Weak Passwords by Reading Users' Minds. USENIX Security 2014. August 20-22, 2014, San Diego, CA, pp. 591-606.
Richard Shay, Saranga Komanduri, Adam L. Durity, Philip (Seyoung) Huh, Michelle L. Mazurek, Sean M. Segreti, Blase Ur, Lujo Bauer, Nicolas Christin, and Lorrie Faith Cranor. Can long passwords be secure and usable? In CHI 2014: Conference on Human Factors in Computing Systems, April 2014. ACM. [Video teaser]
M.L. Mazurek, S. Komanduri, T. Vidas, L. Bauer, N. Christin, L.F. Cranor, P.G. Kelley, R. Shay, and B. Ur. Measuring Password Guessability for an Entire University. ACM CCS 2013.
J. Blocki, S. Komanduri, A. Procaccia, and O. Sheffet. 2013. Optimizing password composition policies. In Proceedings of the fourteenth ACM conference on Electronic commerce (EC '13). ACM, New York, NY, USA, 105-122.
P.G. Kelley, S. Komanduri, M.L. Mazurek, R. Shay, T. Vidas, L. Bauer, N. Christin and L.F. Cranor. The impact of length and mathematical operators on the usability and security of system-assigned one-time PINs. USEC 2013.
B. Ur, P.G. Kelley, S. Komanduri, J. Lee, M. Maass, M. Mazurek, T. Passaro, R. Shay, T. Vidas, L. Bauer, N. Christin, and L.F. Cranor. How does your password measure up? The effect of strength meters on password creation. USENIX Security 2012.
R. Shay, P.G. Kelley, S. Komanduri, M. Mazurek, B. Ur, T. Vidas, L. Bauer, N. Christin, L.F. Cranor. Correct horse battery staple: Exploring the usability of system-assigned passphrases. SOUPS 2012.
Patrick Gage Kelley, Saranga Komanduri, Michelle L. Mazurek, Rich Shay, Tim Vidas, Lujo Bauer, Nicolas Christin, Lorrie Faith Cranor, Julio Lopez. Guess again (and again and again): Measuring password strength by simulating password-cracking algorithms. 2012 IEEE Symposium on Security and Privacy (Oakland) [CyLab Technical Report cmu-cylab-11-008, August 21, 2011.]
Saranga Komanduri, Richard Shay, Patrick Gage Kelley, Michelle L. Mazurek, Lujo Bauer, Nicolas Christin, Lorrie Faith Cranor, and Serge Egelman. Of passwords and people: Measuring the effect of password-composition policies. In CHI 2011: Conference on Human Factors in Computing Systems, May 2011. CHI 2011 Honorable Mention.
Eiji Hayashi, Jason Hong, and Nicolas Christin. Security through a Different Kind of Obscurity: Evaluating Distortion in Graphical Authentication Schemes. In CHI 2011: Conference on Human Factors in Computing Systems, May 2011.
Encountering Stronger Password Requirements: User Attitudes and Behaviors. Richard Shay, Saranga Komanduri, Patrick Gage Kelley, Pedro Giovanni Leon, Michelle L. Mazurek, Lujo Bauer, Nicolas Christin and Lorrie Faith Cranor. SOUPS 2010.
Eiji Hayashi, Nicolas Christin, Rachna Dhamija, and Adrian Perrig Use Your Illusion: Secure Authentication Usable Anywhere. In Proceedings of the Fourth Symposium on Usable Privacy and Security (SOUPS'08). Pittsburgh, PA. July 2008
C. Kuo, S. Romanosky, and L. Cranor. Human Selection of Mnemonic Phrase-Based Passwords. In Proceedings of the 2006 Symposium On Usable Privacy and Security, 12-14 July 2006, Pittsburgh, PA.